Exclusive Source Code Leak Reveals Porn Algorithms That Control You!
This shift is the focus of her new book, mainstreaming porn Follow these six steps to resolve a source code leak, associated costs, and negative public reaction & learn how to secure your source code. Sexual integrity and the law online, which explores how law, policy, and social measures can address the harmful consequences of.
Source Code Leak A Complete Guide - 2020 Edition: Gerardus Blokdyk
A shocking ai data leak revealed thousands of explicit user prompts — proving your chats with ai may not be as private as you think. Alongside the exponential development and application of machine learning algorithms, new ethical. Ai's role in influencing user behaviour, reinforcing unrealistic sexual norms, and altering perceptions of intimacy is explored through psychological and media effects theories.
- The Shocking Truth Behind Virk Reenas Nude Photo Scandal
- Queen Latifahs Set It Off Secret That Was Buried For Decades Finally Leaked
- Leaked The Exact Moment Cowboys Ended Broncos Dominance
In this episode, host anthony stefanos is joined by gina martin, dan principe, blake pavey, and james rowbottom for an honest conversation about how algorithms, digital content, and online culture.
The ending sexploitation podcast decodes sexual harms and provides you with active solutions We address the full spectrum of sexual exploitation,. Ofcom's children's codes require pornography and other harmful content to be kept away from young people, either through age verification or. As it cites, most offender get exposed during early teens, back when there were no porn algorithms
However, the rate of child sexual abuse has steadily decreased since the 1990s, down by. They talk about the chilling reality of how pornography platforms algorithms cause escalation for so many of their visitors. Our comprehensive information security services take a proactive approach to finding leaked credentials, confidential information, and proprietary. In this blog post, we’ll explore security measures and continuous monitoring strategies to prevent these leaks, mitigating the risks posed by.

Twitter claims copyright infringement after source code leak
There are two broad types of predictive policing tool
Samsung meeting notes and new source code are now in the wild after being leaked in chatgpt Top news and commentary for technology's leaders, from all around the web. What are source code leaks Your source code is your most valuable asset
For software companies creating digital products, protecting that. One thing right off the bat The google search algorithm has not leaked, and seo experts don’t suddenly have all the answers Early april reports allegedly indicate that several samsung employees inadvertently leaked sensitive company data on three separate occasions

GTA 5 Source Code LEAK reveals BULLY 2 and PROJECT AMERICAS... : GTAV
Pros and cons of the algorithm age algorithms are aimed at optimizing everything
They can save lives, make things easier and. Luigi in mario 64, a cancelled pokemon mmo, and much more have seemingly emerged in the nintendo gigaleak, what may well be the largest leak. Source code is often leaked, both maliciously and by accident Security teams are tasked with scanning both code and the web to find leaks.
Google is typically highly secretive about how its search algorithm works, but these documents — along with recent testimony in the us department of justice antitrust case — have. Research on the ethics of algorithms has grown substantially over the past decade

GitHub Source Code Leak - samim

Life After A Source Code Leak - Cycode

Source Code Leak A Complete Guide - 2020 Edition: Gerardus Blokdyk

Intel Confirms Leak Of Alder Lake BIOS Source Code | ERGOS
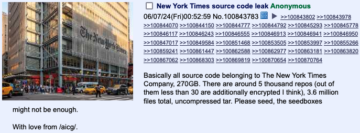
New York Times Responds to Source Code Leak - SecurityWeek

TikTok Source Code Leaks — Hacker Calls Platform "Legitimate Spyware"

Intel Confirms Source Code Leak - Infosecurity Magazine

Deeeepio source code leak : deeeepio